Decrypt Keychain.plist
How to decrypt an encrypted Apple iTunes iPhone backup? Ask Question. Up vote 75 down vote favorite. I've been asked by a number of unfortunate iPhone users to help them restore data from their iTunes backups. This is easy when they are unencrypted, but not when they are encrypted, whether or not the password is known. As such, I'm. Decrypting.plist file that was encrypted on device? I have access to the keychain on the device and suspect this was used in the. Encrypt/decrypt.plist file ios. Calculate a hash (aka message digest) of data. Implementations are from Sun (java.security.MessageDigest) and GNU. If you want to get the hash of a file in a form that is easier to use in automated systems, try the online md5sum tool.
Decrypt Keychain
I've been asked by a number of unfortunate iPhone users to help them restore data from their iTunes backups. This is easy when they are unencrypted, but not when they are encrypted, whether or not the password is known. As such, I'm trying to figure out the encryption scheme used on mddata and mdinfo files when encrypted.
I have no problems reading these files otherwise, and have built some robust C# libraries for doing so. (If you're able to help, I don't care which language you use. It's the principle I'm after here!) The Apple 'iPhone OS Enterprise Deployment Guide' states that 'Device backups can be stored in encrypted format by selecting the Encrypt iPhone Backup option in the device summary pane of iTunes. Files are encrypted using AES128 with a 256-bit key. The key is stored securely in the iPhone keychain.' That's a pretty good clue, and there's some good info here on Stackoverflow on iPhone suggesting a keysize of 128 and CBC mode may be used. Aside from any other obfuscation, a key and initialisation vector (IV)/salt are required.
One might assume that the key is a manipulation of the 'backup password' that users are prompted to enter by iTunes and passed to ', padded in a fashion dictated by CBC. However, given the reference to the iPhone keychain, I wonder whether the 'backup password' might not be used as a password on an X509 certificate or symmetric private key, and that the certificate or private key itself might be used as the key.
Decrypt Keychain Plist
( and the iTunes encrypt/decrypt process is symmetric.) The IV is another matter, and it could be a few things. Perhaps it's one of the keys into iTunes, or into the. Although Apple's comment above suggests the key is present on the device's keychain, I think this isn't that important. One can restore an encrypted backup to a different device, which suggests all information relevant to the decryption is present in the backup and iTunes configuration, and that anything solely on the device is irrelevant and replacable in this context.
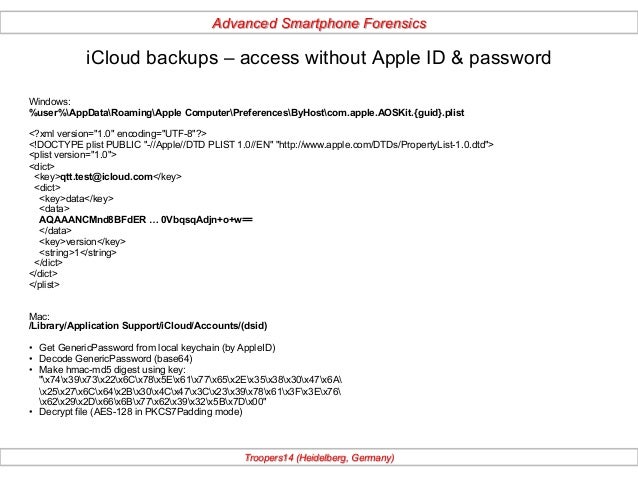
So where might be the key be? I've listed paths below from a Windows machine but it's much of a muchness whichever OS we use. The ' appdata Roaming Apple Computer iTunes itunesprefs.xml' contains a PList with a 'Keychain' dict entry in it. The ' programdata apple Lockdown 09037027da8f4bdefdea97d706703ca034c88bab.plist' contains a PList with 'DeviceCertificate', 'HostCertificate', and 'RootCertificate', all of which appear to be valid X509 certs. The same file also appears to contain asymmetric keys 'RootPrivateKey' and 'HostPrivateKey' (my reading suggests these might be PKCS #7-enveloped). Also, within each backup there are 'AuthSignature' and 'AuthData' values in the Manifest.plist file, although these appear to be rotated as each file gets incrementally backed up, suggested they're not that useful as a key, unless something really quite involved is being done.
There's a lot of misleading stuff out there suggesting getting data from encrypted backups is easy. It's not, and to my knowledge it hasn't been done. The backup encryption is another matter entirely, and is not what I'm looking to do.
This isn't about hacking apart the iPhone or anything like that. All I'm after here is a means to extract data (photos, contacts, etc.) from encrypted iTunes backups as I can unencrypted ones. I've tried all sorts of permutations with the information I've put down above but got nowhere. I'd appreciate any thoughts or techniques I might have missed. Sorry, but it might even be more complicated, involving pbkdf2, or even a variation of it. Listen to the WWDC 2010 session #209, which mainly talks about the security measures in iOS 4, but also mentions briefly the separate encryption of backups and how they're related.
Rats of nimh. You can be pretty sure that without knowing the password, there's no way you can decrypt it, even by brute force. Let's just assume you want to try to enable people who KNOW the password to get to the data of their backups. I fear there's no way around looking at the actual code in iTunes in order to figure out which algos are employed.
Back in the Newton days, I had to decrypt data from a program and was able to call its decryption function directly (knowing the password, of course) without the need to even undersand its algorithm. It's not that easy anymore, unfortunately. I'm sure there are skilled people around who could reverse engineer that iTunes code - you just have to get them interested. In theory, Apple's algos should be designed in a way that makes the data still safe (i.e. Practically unbreakable by brute force methods) to any attacker knowing the exact encryption method.
And in WWDC session 209 they went pretty deep into details about what they do to accomplish this. Maybe you can actually get answers directly from Apple's security team if you tell them your good intentions.
After all, even they should know that security by obfuscation is not really efficient. Try their security mailing list. Even if they do not repond, maybe someone else silently on the list will respond with some help. Yes, and I've read the source, too. It does not handle encrypted backups, and was last modified prior to release of iTunes' support for encrypted backups. I suspect you mean your backups are encoded or that your iPhone uses an encrypted filesystem, which is another matter entirely.
As well as there being no support for encryption in the code, more obviously there's no option to pass in a password in the command-line options. And the code doesn't use any certs or keychains. I'd love to be proven wrong on this, but I really don't think I am!
I appreciate the suggestion, though. – Oct 2 '09 at 13:01.
In iTunes backup, the iPhone Keychain sqlite database is stored as a Plist file. The Keychain file gets stored with 51a4616e576dd33cd2abadfea874eb8ff246bf0e file name in the iTunes backup folder. Keychain data stored in the backup is encrypted using a hardware generated key – key 0x835. So renaming the file 51a4616e576dd33cd2abadfea874eb8ff246bf0e to keychain-backup.plist and editing with a plist editor opens the file but does not display the data in it. Steps to decrypt the backup Keychain (Mac OS X): 1. Go to iTunes backup folder. Default location is -/Library/Application Support/MobileSync/Backup/ 2.
Rename the file 51a4616e576dd33cd2abadfea874eb8ff246bf0e to keychain-backup.plist. Extract key 0x835 by following my previous blog post –. 4. Download & install. Researchers at sogeti developed tools to decrypt the keychain files. Grab the tools by running the below command on Mac OS X terminal.
Install python dependencies. Sudo easyinstall M2crypto construct progressbar setuptools sudo ARCHFLAGS='-arch i386 -arch x8664' easyinstall pycrypto 6. Navigate to iphone-dataprotection folder and run keychaintool.py by supplying keychain-backup.plist path and the backup folder path. The script prompts for key 0x835. Key in the value obtained in step 2. Keychain-tool.py automatically decrypts the backup keychain content and displays it on the terminal.
Steps to decrypt the backup Keychain (Windows 7): 1. Go to iTunes backup folder. Default location is – C: Users user name AppData Roaming Apple Computer MobileSync Backup 2. Rename the file 51a4616e576dd33cd2abadfea874eb8ff246bf0e to keychain-backup.plist. Extract key 0x835 by following my previous blog post –. 4. Download & install. Researchers at sogeti developed tools to decrypt the keychain files.
Grab the tools by running the below command from windows command prompt. It creates iphone-dataprotection folder in the current directory. Download and install in C: Python26 folder. Add C: Python26 to system PATH environment variable.
Install windows. Install python dependencies –, & 9. Download and extract it to c: drive. From command prompt navigate to c: progressbar-2.3 and type the below command. Cd progressbar-2.3 python setup.py install 10. Download and extract it to c: drive. From command prompt navigate to c: construct-2.06 folder and type the below command. Cd construct-2.06 python setup.py install 11.
From command prompt, navigate to iphone-dataprotection folder and run keychaintool.py by supplying keychain-backup.plist path and the backup folder path. Cd iphone-dataprotection python pythonscripts/keychaintool.py C: Users user name AppData Roaming Apple Computer MobileSync Backup UDID keychain-backup.plist C: Users user name AppData Roaming Apple Computer MobileSync Backup UDID Manifest.plist. In the above command replace user name & UDID with appropriate values. The script prompts for key 0x835. Key in the value obtained in step 2. Keychain-tool.py automatically decrypts the backup keychain content and displays it on the command prompt. Note: keychain in the iTunes encrypted backup is stored encrypted with iTunes password.
Decrypt Keychain Plist
So while decrypting the keychain from iTunes encrypted backups, enter the backup password instead of key 0x835. More detailed video demonstration is available at –. For iOS 7, apply this patch –.